🛑 How I Discovered Sensitive Student Info on a Government Education Portal! 🛑
-
 ###### How I Discovered Sensitive Student Info on a Government Education Portal!
###### How I Discovered Sensitive Student Info on a Government Education Portal! 
Hey Community!

I was doing some basic security research on a few local domains and stumbled upon a serious Information Disclosure vulnerability. I wanted to share my findings (without naming the exact target for security reasons) to highlight how critical API security is.
The Target: [A Sri Lankan Government Educational Portal]
Vulnerability Type: Broken Object Level Authorization (BOLA) / Unprotected API Endpoint.
How to do it step by step?
 ️
️ ️
️-
Random Selection
 I decided to check the security posture of a well-known educational portal in Sri Lanka. I started by exploring the site’s structure and how it handles data requests.
I decided to check the security posture of a well-known educational portal in Sri Lanka. I started by exploring the site’s structure and how it handles data requests. -
Identifying the Attack Surface
 While browsing, I noticed the site was using an API to fetch some front-end data. This piqued my curiosity.
While browsing, I noticed the site was using an API to fetch some front-end data. This piqued my curiosity. -
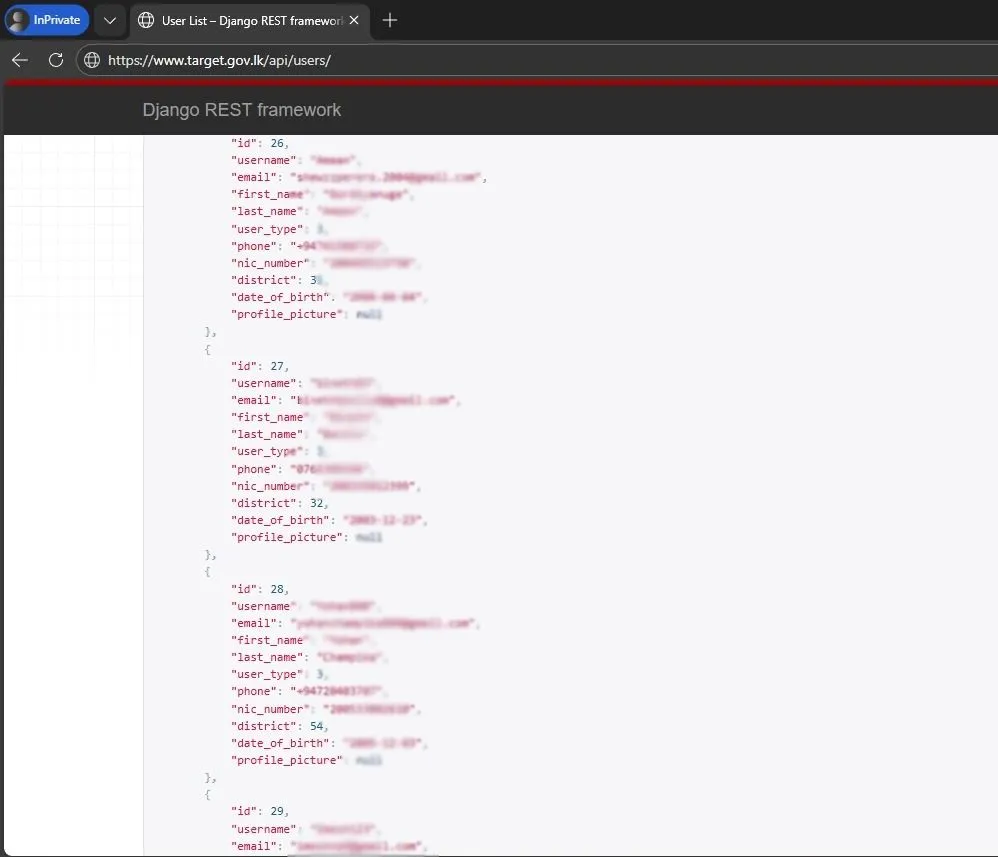
🧪 I tried to guess common API endpoints. Instead of navigating the UI, I manually appended a common path to the root URL: https://[target_site].gov.lk/api/users/
-
The Success (Data Exposure)
 To my absolute shock, the server didn't ask for a login or a token. It responded with a massive JSON array containing:
To my absolute shock, the server didn't ask for a login or a token. It responded with a massive JSON array containing:Full Names / Emails/ Mobile numbers / Birthdays / Nic numbers of Students

Why Is This Dangerous?
 ️
️No Authentication: The API endpoint was completely public. Anyone with the link could download the entire user database. Massive Privacy Breach: Thousands of students' personal info could be harvested by bots within seconds. 🤖 Identity Theft: This data is a goldmine for phishers and scammers targeting students. 🎣How to Fix This? (For Admins)
 ️
️Implement Authentication: Never leave /api/ endpoints open. Use JWT or API keys. Rate Limiting: Prevent automated scripts from scraping the entire database. Role-Based Access Control (RBAC): Ensure that only authorized admins can access the /users/ list.Conclusion

This just goes to show that you don't always need complex tools to find a "hole" in a system. Sometimes, a simple URL tweak is all it takes. I hope the developers of this site fix this ASAP!

What do you guys think? Is API security being ignored in our local gov-tech sector? Let’s discuss below!

#CyberSecurity #LK #BugBounty #InfoSec #DataPrivacy #EthicalHacking #AnonSathaN #SriLanka
-
-
ලංකාවේ දැනට තියෙන ගොඩක් government sites වල මේ කේස් එක තියෙන්වා.

