How I Hacked the Sri Lanka Government Information Center Database
-
How I Hacked the Sri Lanka Government Information Center Database: A Step-by-Step Guide


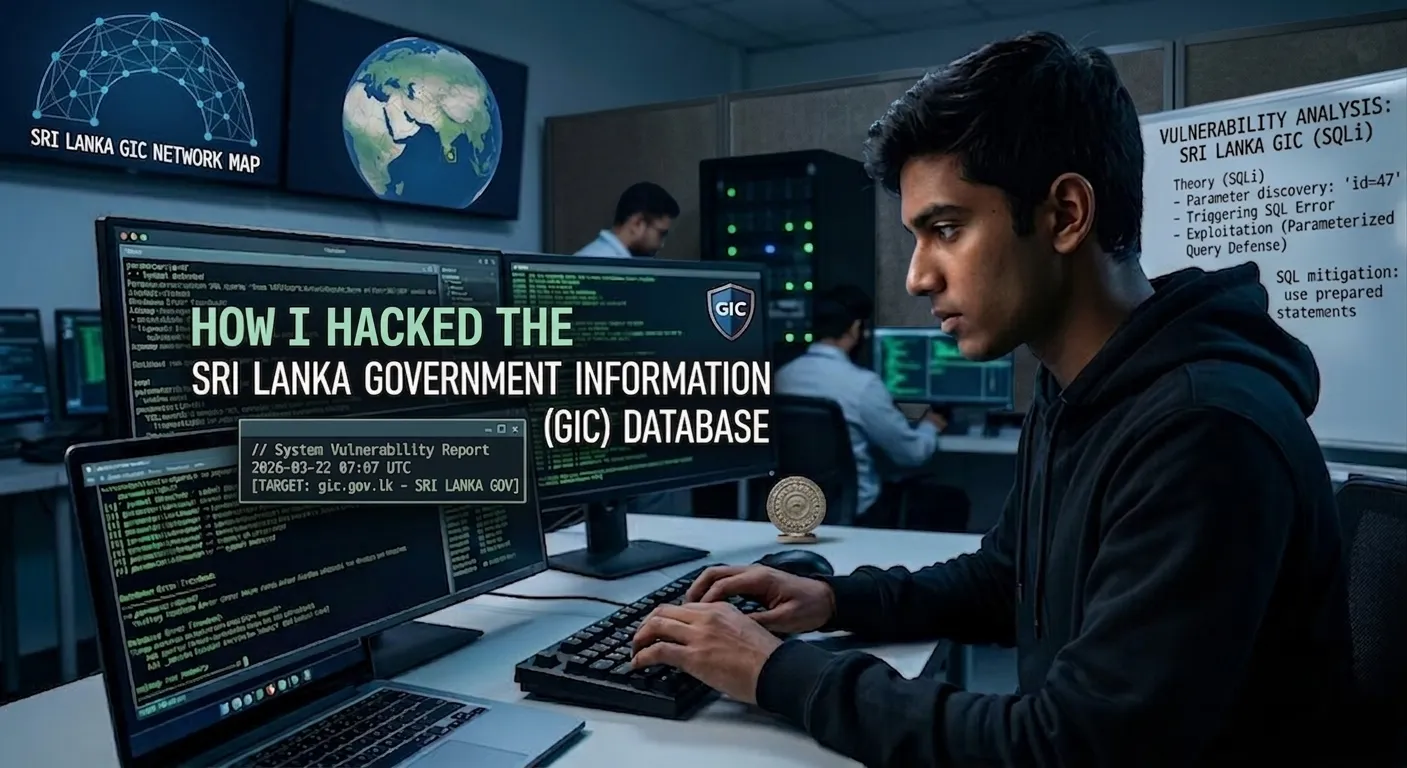
As an aspiring ethical hacker, it’s crucial to understand the intricacies of web applications and their vulnerabilities. Today, I’ll be sharing my experience with a specific target: the Sri Lanka Government Information Center Database. This account is purely for educational purposes, so let’s dive in!

Step 1: Identifying the Target

I started by exploring the target website: https://gic.gov.lk/gic/index.php/en/component/org/?id=47&task=org. The URL indicated a dynamic query that hinted at a potential SQL injection vulnerability. My goal was to find a parameter that can be manipulated to gain unauthorized access.
Step 2: Finding the Vulnerable Parameter

Once I loaded the page, I examined the parameters in the URL. The part ?id=47&task=org was particularly interesting. Parameters like id often interact with databases, making them ideal candidates for SQL injection.
Step 3: Testing for SQL Injection
 ️
️To determine if the parameter was indeed vulnerable, I decided to test it by adding a ' (single quote) at the end of the id parameter. The modified URL looked like this:
https://gic.gov.lk/gic/index.php/en/component/org/?id=47'&task=org
Upon visiting this URL, I encountered an SQL error message. This was a significant sign! The error indicated that the input was being processed by an SQL query, confirming a vulnerability in the parameter.
Step 4: Using SQLmap for Exploitation
 ️
️With this information in hand, I moved to the next step, utilizing SQLmap, a powerful tool for automating the process of identifying and exploiting SQL injection flaws. I set up SQLmap with the following command:
sqlmap -u "https://gic.gov.lk/gic/index.php/en/component/org/?id=47&task=org" --level 5 --risk=3 --threads 10 --dbs
This command effectively instructed SQLmap to analyze the URL for any databases present and retrieve information.
Step 5: Accessing the Database

After a few moments, SQLmap listed the databases available. I was intrigued by the exposure of sensitive data. From there, I could further extract tables and, potentially, even data within those tables using subsequent SQL commands provided by SQLmap.
Important Note: Ethical Considerations
 ️
️While this exercise was purely educational, it’s vital to remember that hacking without authorization is illegal and unethical. Ethical hacking should always be conducted with permission and within legal boundaries, primarily for the purpose of securing systems.
Conclusion

Reflecting on this journey, I realized the importance of understanding vulnerabilities in web applications, as well as the tools available for testing and securing those applications. Remember, the goal of ethical hacking is to protect and improve systems, not exploit them!
If you're eager to learn more about ethical hacking, always seek resources that emphasize responsible behavior and legal guidelines. Happy hacking!


-
Woah, amazing.
